2024-05-01 / Posts
2024-02-27 / Talks
2024-02-01 / Publications
2023-08-30 / Publications
Our mission urges us to consider problems across multiple subject areas, both applied and theoretical. We pursue these problems in the open and share our results in recorded talks and published papers.
Learn moreWe aim to use learnings from previous efforts, growth in available data, and ambitions of qualitatively novel capabilities to facilitate the discovery, linking, and processing of knowledge. This work primarily consists of support for The Underlay, a project intending to build a global, distributed graph of public knowledge.
A long-term goal for the IPFS ecosystem is to merge distributed apps and local apps into a single paradigm: fundamentally rethinking the UNIX programming model for a content-addressable platform. As a component of this, we aspire to make the best use of state-of-the-art advances in programming language design and implementation, such as substructural types, modal types, and algebraic effects.
Category theory (CT) originated as a subdiscipline of pure mathematics, with a historical strength in unifying disparate mathematical areas to transport proofs and constructions between them. CT can also be viewed as an upgraded foundation for all of math, taking the place traditionally occupied by first-order logic and set theory, and is commonly used in theoretical computer science (especially type theory), and as a foundation for computational theorem-proving.
Distributed systems are, broadly speaking, networked systems whose components are located in different nodes that communicate and coordinate to achieve the system’s purpose. Distributed systems are at the very core of what we do and our interests extend across the entire field.
Modern cryptography plays an integral role in every aspect of online and electronic security, including providing evidence you’re speaking to the intended party and hindering spying on the subsequent communication. Cutting-edge cryptography tools will allow the creation of incredibly strong evidence that general information processing has been performed in a privacy-preserving and trustless way.
In any forum or marketplace where people can interact, the venue itself guides and constrains human interaction. Cryptoeconomics provides practices, tools, and knowledge that allow us to engineer the venue to achieve a goal.
Our electricity system is undergoing a monumental transition from a centralized design based on fossil fuels to a distributed architecture based on renewable energy. Successfully navigating this requires reconceiving the grid as a distributed system, able to coordinate diverse resources and influence the deployment of capital by setting up appropriate incentive structures.
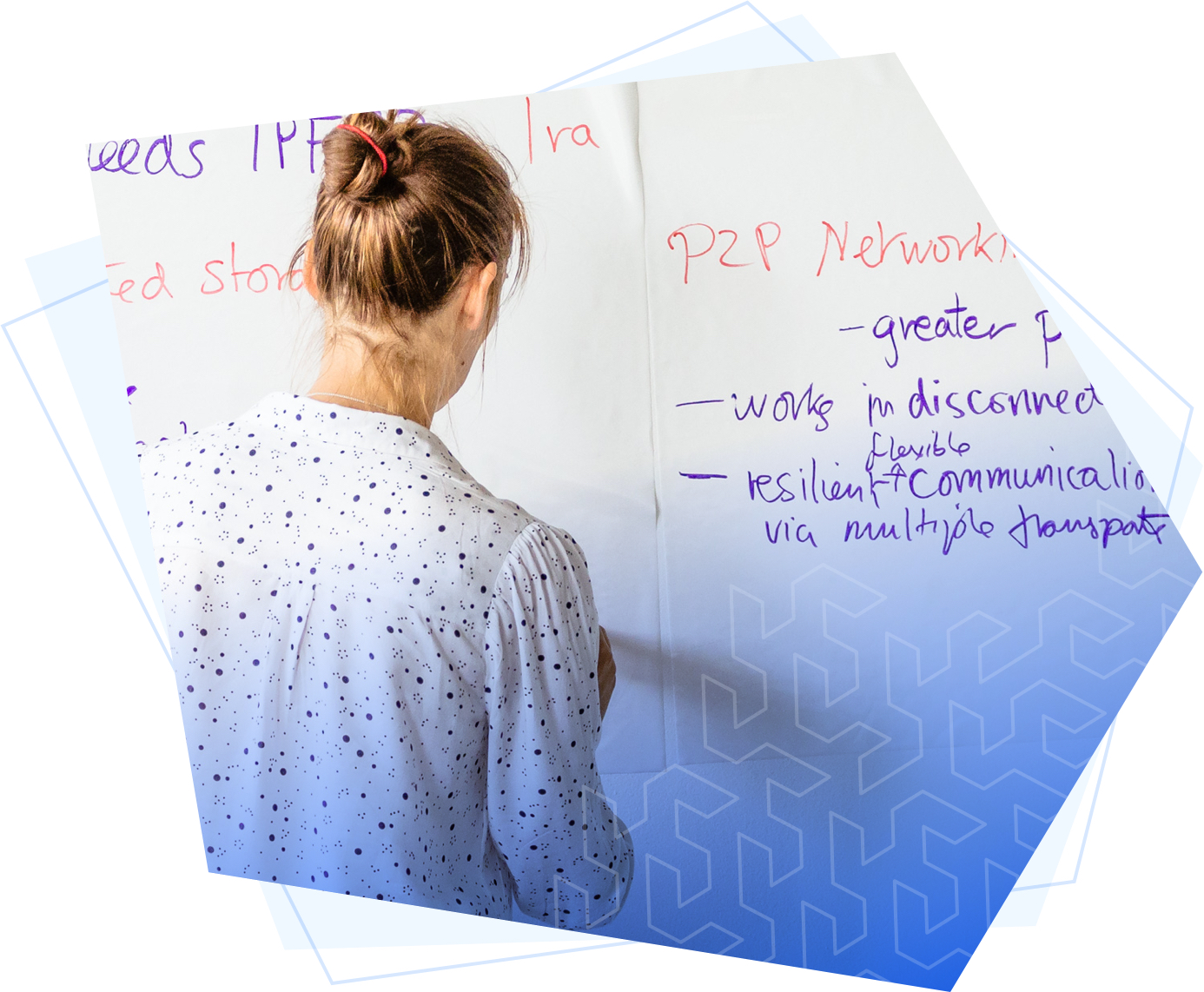
Computer networks enable information to move across the globe. They are foundational to the world we live in and to the vast majority of our work. Our interests include transport and routing protocols, network security, p2p systems, publish-subscribe protocols, and network monitoring and simulation.
Metaresearch is the investigation of how scientific innovation occurs. It encompases work in the history, philosophy, and economics of science; the effects of incentive systems in research; the evaluation and validation of scientific data; and the dissemination of scientific knowledge, among other fields.

We're a fully remote team distributed across the globe. We work with talented and intellectually curious people of diverse backgrounds and perspectives who share a passion for improving technology for humanity.